Continuous ∞ security for <any> team
Instant external scans and continuous monitoring — for teams focused on data safety and secure development without breaking the budget
Open-source power, <zero setup>
We packaged well-known open source solutions into a ready-to-use cost-saving solution for you
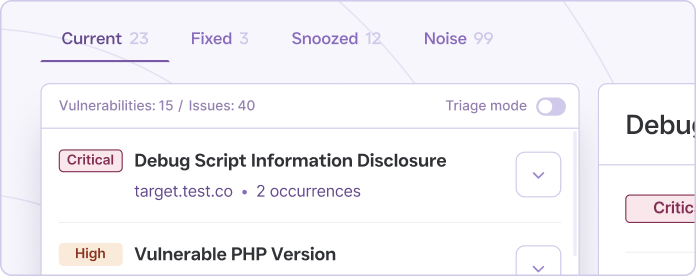
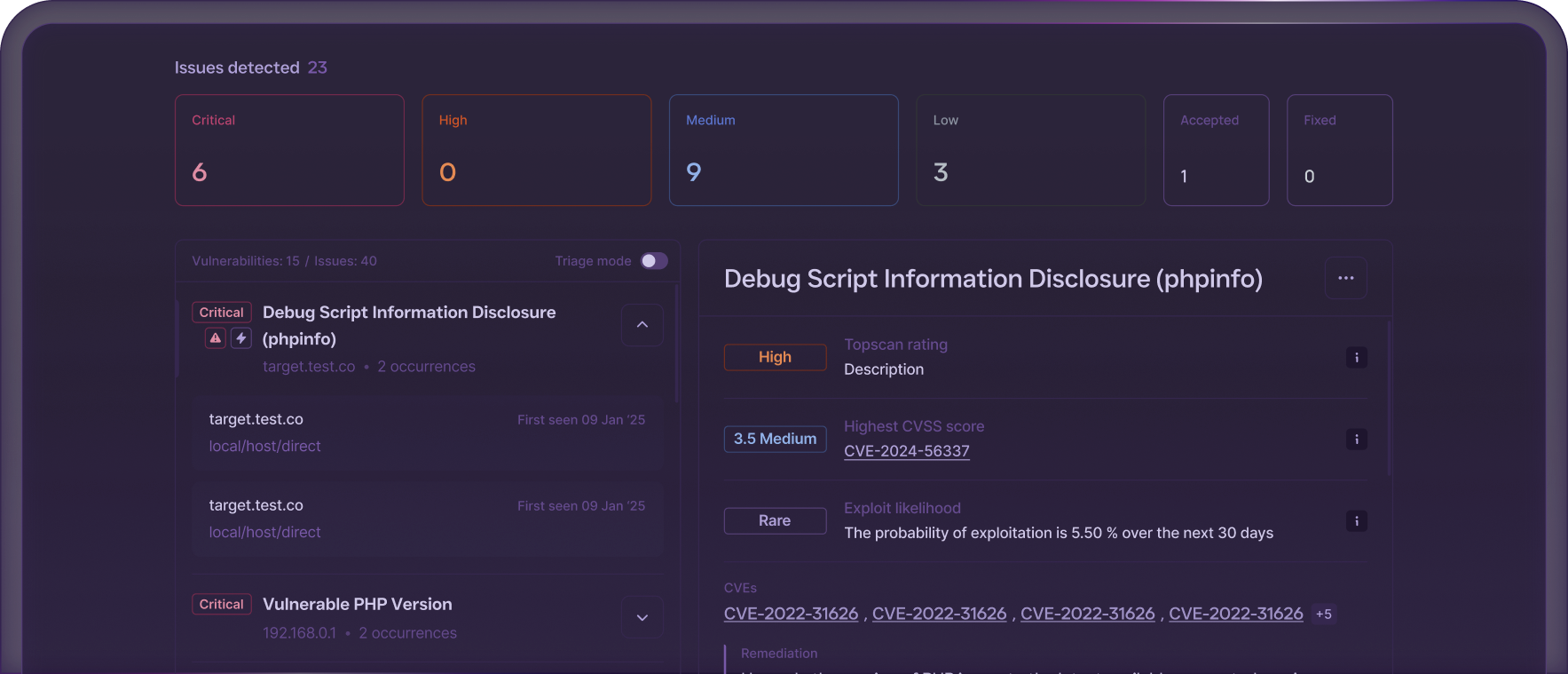
Forget digging through raw reports — we preprocessed and grouped vulnerabilities for you
Highlighted what matters most
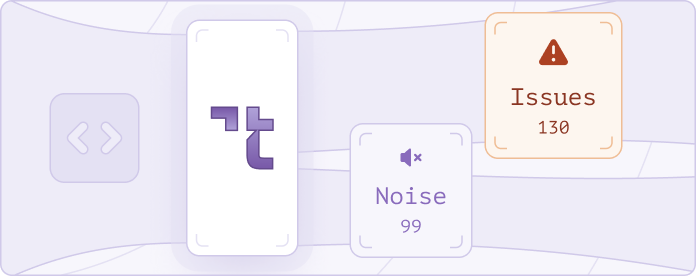
And filtered out noise
Five minutes to <start> your security scans
Quick start: Sign up with Google or Github. Just 5 min from registration to the first scan!
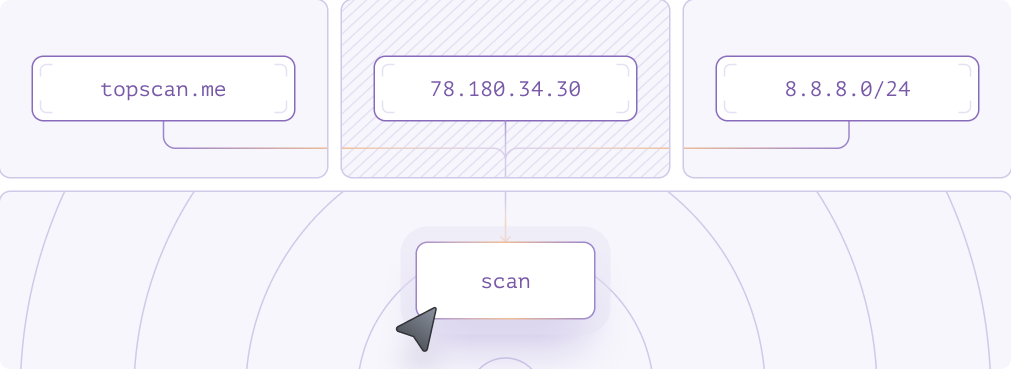
Fast setting a scan: add your targets (IP, CIDR, domains), and start scanning
Yes, even <for free>
14-day trial with full functionality. No card required!
Just register and start full functional vulnerability scans.
Integrate scans directly in your <pipeline> and run them with <webhooks>


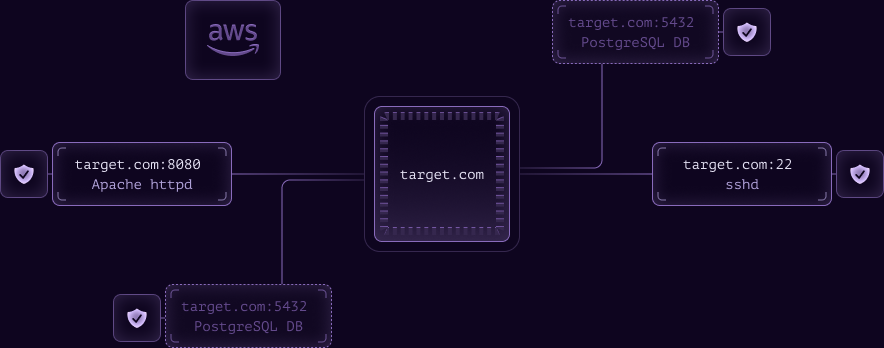
Attack surface discovery, always <up to date>
Auto-discover services, IPs, sub-domains, and cloud endpoints & Add them to your scan list and dashboard without manual work
Fair pricing for <your security>
From startups to enterprises — one fair model for all security teams

Pay per target,
not per user or scan

Unlimited rescans
and free read-only seats for auditors
FAQ
Topscan builds on the best in class scanning engines
Still have questions?
Contact usTopscan uses a well-known open source solution, such as Owasp Zap and Nuclei. But Topscan was built as a platform for infrastructure security management, and it can work with any other scanner's report.
Modern internet services have many dependencies, and no one is immune to errors in third-party software. Constant monitoring can minimize the risk of external intrusion.